An In-Depth Guide to Remote Desktop Protocol (RDP)
The continually changing nature of today's workplace has made remote access technology essential.
The continually changing nature of today's workplace has made remote access technology essential.

The continually changing nature of today’s workplace has made remote access technology essential. The Remote Desktop Protocol (RDP) is an important technology that facilitates smooth remote access.
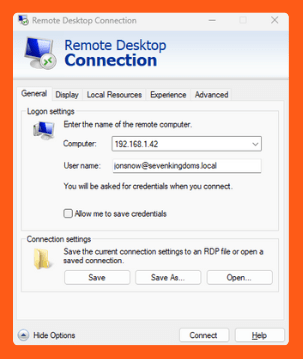
Microsoft created the Remote Desktop Protocol (RDP), which enables users to connect to another computer via a network and view a graphical user interface. Through Remote Desktop Protocol (RDP), a user may access a remote computer’s desktop and apps just like they would if they were in front of it. Since its first introduction in 1998 as part of Windows NT 4.0 Terminal Server Edition, this technology has transformed into a widely used tool for remote access and management.
RDP’s primary objective in our day-to-day is to make remote work, technical help, and administrative tasks easier. Helpdesk teams use it to diagnose problems without requiring physical access to the equipment. IT professionals use it to remotely manage servers and workstations, while businesses use it to allow employees to work from their homes.
RDP works through a client-server architecture. The RDP server is installed on the computer that must be accessed remotely, and the RDP client is installed on the device that connects to it. The user’s input, which consists of keyboard and mouse clicks, is captured by the client software and sent to the server, which processes it and returns the graphical result to the client. This is usually done using port 3389, the default port for RDP traffic assigned by Microsoft.
Due to it being a common port, using it as the RDP port can pose security risks. Cyber attackers often scan for open ports to find potential targets to perform brute-force attacks and other malicious activities.
RDP has a variety of features that make it an effective tool for remote access and management. Some of the important aspects are:
RDP has several practical applications across multiple sectors and use cases. Some common applications include:
While RDP provides numerous advantages, it also introduces security vulnerabilities that must be addressed to provide safe and secure remote access. Some typical security vulnerabilities related to RDP include:
To reduce these risks, it is important to implement these best practices for securing RDP.
Although RDP is a widely used option for remote access, there are several other alternatives as well, each with unique features and advantages.
Swarm Intelligence: Stryker’s Intune wipe proves your BCDR plan has a single point of failure
Your IT team uses Intune to manage devices. So did the attacker who wiped Stryker’s hospital infrastructure. No malware. No ransomware. No exploit chain. Just one…

Dynamic Attack Surfaces: The Professional Sports Problem
Professional sports organizations face cybersecurity challenges that don’t fit traditional frameworks. With seasonal spikes, constant third-party integrations, and workforce volatility, annual pen tests capture one snapshot…

Claude Jailbroken To Attack Mexican Government Agencies
A threat actor jailbroke Claude to orchestrate a month-long attack on Mexican government networks, stealing 150 GB of sensitive data. We analyze what really happened and…